
- POSITION
- Associate Prof.
- kwondh@pusan.ac.kr
- Lab.
- Computer Security Lab.
1. Research Area
CSL (Computer Security Laboratory) conducts security research for software running on various computing devices such as embedded devices, mobile devices, and server machines. For this, we basically use techniques in compiler, operating system and computer architecture. But we are open to any new types of techniques to enhance the security of the computing systems. Also, we are studying new attack vectors for various software such as deep learning engine, blockchain wallet and browser. If you have any interests in the system security, please contact us.
2. Research Overview
- Embedded System Security
Compared to resource-rich computing devices such as PC and Server, many embedded systems are resource-constraint in terms of computing power and cost. Thus, embedded systems have been supported with less security features. However, with the growth of the Internet of Things (IoT) technologies, the security of embedded systems is getting more and more important. To deal with this problem, CSL are implementing various security solutions that enhance the security level of these devices while assuming those constraints.
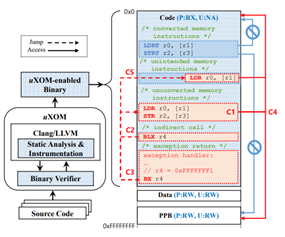
Figure 1. Overview of uXOM presented in USENIX Security’19
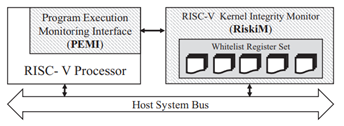
Figure 2. Overview of RiskiM presented in DATE’19
- Hardware-assisted System Security
RISC-V is a free and open source Instruction set architecture. By utilizing thes properties, we are implementing several hardware-based security solutions. Specifically, we have proposed an external hardware module (see bellow figure) to monitor the integrity of the OS kernel running on the target processor and also we are working on developing a new instruction extension for the system security.
3. Research Achievements
- Representative publication list (at June 2020)
- Donghyun Kwon, Jiwon Seo, Yeongpil Cho, Byoungyoung Lee, Yunheung Paek, PrOS: Light-weight Privatized Secure OSes in ARM TrustZone (to appear), (SCI) IEEE Transactions on Mobile Computing (TMC) 2020 (IF: 3.822)
- Donghyun Kwon, Jangseop Shin, Giyeol Kim, Byoungyoung Lee, Yeongpil Cho, Yunheung Paek, uXOM: Efficient eXecute-Only Memory on ARM Cortex-M, Usenix Security 2019 (acceptance rate: 18.9%)
- Donghyun Kwon, Hayoon Yi, Yeongpil Cho, Yunheung Paek, Safe and Efficient Implementation of a Security System on ARM using Intra-Level Privilege Separation, (SCIE) ACM Transactions on Privacy and Security (TOPS) 2019 (IF: 1.714)
- Dongil Hwang, Myunghoon Yang, Seongil Jeon, Younghan Lee, Donghyun Kwon, Yunheung Paek, RiskiM: Toward Complete Kernel Protection with Hardware Support, Design, Automation and Test in Europe (DATE) 2019 (acceptance rate: 24%)
- Jangseop Shin, Donghyun Kwon, Jiwon Seo, Yeongpil Cho, Yunheung Paek, CRCount: Pointer Invalidation with Reference Counting on Mitigate Use-After-Free in Legacy C/C++, Network and Distributed System Security Symposium (NDSS) 2019 (acceptance rate: 17.1%)
* For further publications: https://sites.google.com/view/csl-pnu/publicationProgram 2020-2025, Surface based analysis of brain magnetic resonance (MR) images.